Introduction
When developing web applications using a server-side framework, use the following procedures to set up your authorization. This tutorial is based on the OAuth workflow, diagram, and steps described in the web app authorization documentation.
Register your application
The first step for authorizing your web app is to register your application.
- If you have not created an application, open the My Apps page under your Profile menu, and click the Register New button. In this case, the application type is Web App.
- For this tutorial, add the redirect URI,
https://developer.bentley.com/redirect-tutorial, during app registration, or on the App Details for a previously registered application. If you are testing locally or on a deployed app, you will use the redirect URI of your application. - Make sure to save the
client_idand theclient_secretsupplied when you create your application.
Obtain an access token
Once you have your app registered, you can obtain an access token by following these steps:
-
Redirect the user to the authorization endpoint.
https://ims.bentley.com/connect/authorize
Below is an example request along with required parameters. You can obtain the client_id and redirect_uri from your app registration on My Apps.
-
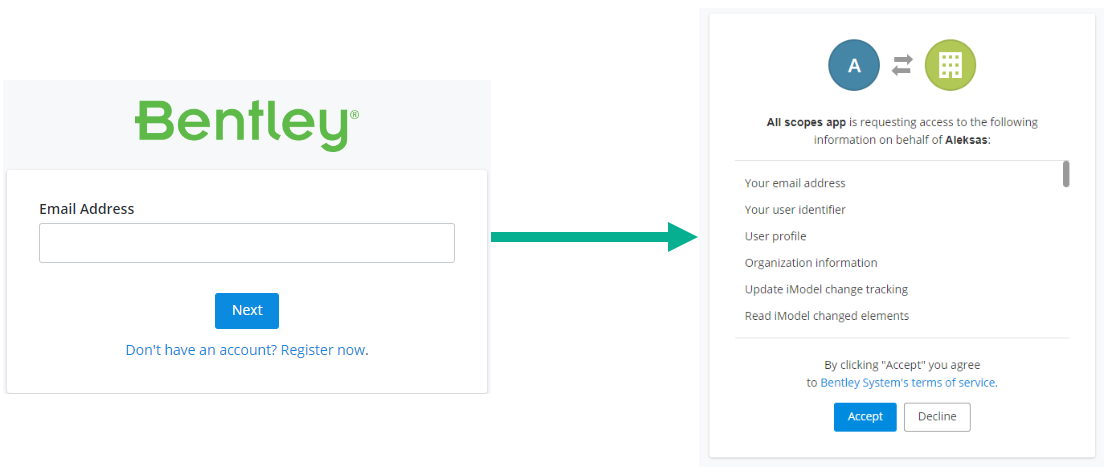
Allow user to login and give consent to the application for calling APIs on their behalf.
-
Once authenticated, extract the
codein the response from theredirect_urithat authorization server is configured to use.https://example-rediect-uri/?code=<code> -
Send a request to the token endpoint to exchange the authorization code for an access token.
Your app's client_secret is one of the required parameters. If you didn't already save your client_secret, generate a new one from your app registration on My Apps.
- Your application can now use the access token returned by the token endpoint to access APIs on behalf of the user.
Request a new access token with a refresh token
When your access token is close to the expiry time, you can request a new one using the refresh token provided in the original request. The response contains a new token and a new refresh token.
Use your token
If you received a 200 OK response to your token request, you have successfully obtained a token. You can use this token to call various iTwin Platform APIs. You can try making an API call to users/me endpoint to test your token. On success, this request returns the profile information for the user account associated with the token received.
Remember, the iTwin Platform Base URI is api.bentley.com.